Code Archaeology
Abstract Software Engineers have to spend a considerable amount of time doing work that is not directly related to writing code. Much of this work falls into a category described here as “Code Archeology“, where the reasons, rationale, structure, and bugs of software must be clearly understood before improvements can be made. This work, which…
Read more
EnvoyProxy 5: Authorized Access with JWT
Abstract The purpose of this article is to explain how to use technologies is to validate that users are who they claim to be (authentication) and to determine what resources that user has permission to access (authorization). This is done by expanding upon the protections against man-in-the-middle and eavesdropping attacks that are obtained with the…
Read more
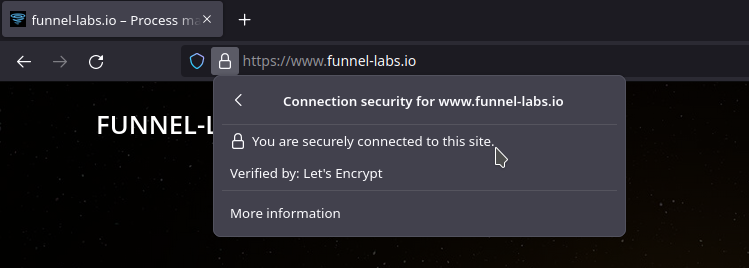
EnvoyProxy 4: Securing Connections with HTTPS
Abstract In order to secure a network system from eavesdropping and man-in-the-middle attacks, it is important to protect your data from outsiders as it travels across the public infrastructure of the Internet. Encryption can be used to shield data from prying eyes and digital signatures can verify that clients are connecting to your web service.…
Read more
Introduction to Network Security
Introduction When building a networked computer system, an inescapable fact that one must contend with, is that a large chunk of the communication between your system and its users will occur over public network infrastructure that you do not own or operate. There is no guarantee that there are not malicious actors who may intercept…
Read more
EnvoyProxy 3: Sophisticated Rate Limiting
Abstract This article continues on the work from the previous article, EnvoyProxy 2, but makes use of a powerful feature, rate limiting, which can block requests if they are made more frequently than a certain limit. A demonstration of using this feature to protect against general brute-force attacks is provided, as well as customizing rate…
Read more
EnvoyProxy 2: Microservices and Routing
Abstract In part 1 of this series of articles on EnvoyProxy, a high level overview of reverse proxies, what they are for, and the internal architecture of EnvoyProxy is explained. Furthermore, the reader was made familiar with how to configure EnvoyProxy and where to find documentation to learn more. In this article, the ways in…
Read more
EnvoyProxy 1: Reverse Proxy
Abstract A proxy server is a server application that acts as an intermediary between a client requesting a resource and a server providing a resource, which typically exists at the edge of the network of the client organization. A reverse proxy sits at the edge of the network of the resource provider’s organization, and is…
Read more
Data Serialization: Apache Avro vs. Google Protobuf
Abstract For applications that need to transmit data over a network or persist data for storage into files, the topic of selecting a data serialization format is an important one. For low performance applications with small amounts of data, there are advantages to using JSON, which is highly readable by humans. However, for more complex…
Read more
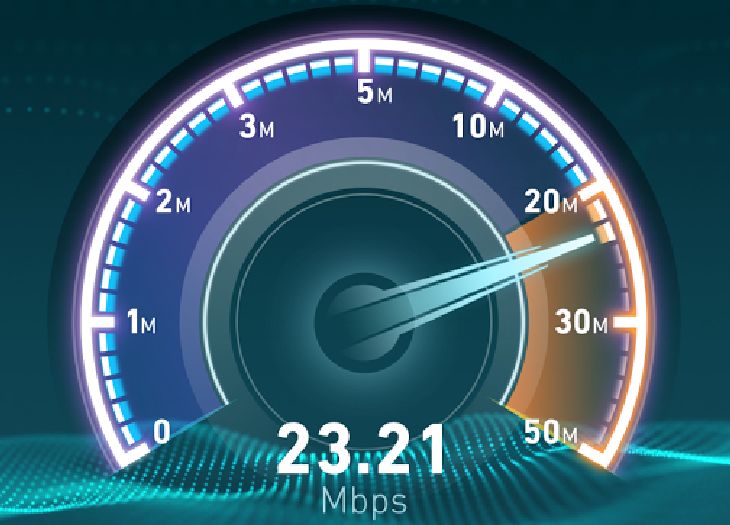
Assessing Performance of Network Systems
Introduction As development of software services moves from a local development environment environment to a staging or production environment, a common concern that arises is to know the limits of what the system can handle in terms of performance. Knowledge of what your system can handle is useful for several reasons: Performance numbers are often…
Read more
Language and Performance: Java and D
Introduction In the previous article, Perspectives on Software Performance, it was discussed how the computational performance and efficient use of RAM can be used to greatly lower the costs associated with solving a given business problem. In this article, the impact of the choice of technology will be further elaborated. This analysis will focus on…
Read more